Release Notes
July 2020
What's New
In our July release, we've added the ability to set up SAML-based SSO using Okta as an identity provider. We’re also introducing two new sections in the devices workflow: A new Summary Tab and redesigned Labels Tab.
In addition, we now offer bootstrap token storage for manually-enrolled macOS devices (10.16, 11.0); the ability to select and schedule OS Updates; and a new capability for certain identity and encryption certificates. There are also new restriction settings available when working with DEP Profiles, iOS 14.0, and macOS 11.0 devices.
Features
SAML-based SSO with Okta
KACE Cloud MDM subscribers can now use Okta when setting up single sign-on (SSO). Configuring SSO to use Okta lets users sign in to KACE Cloud MDM using their managed Okta accounts.
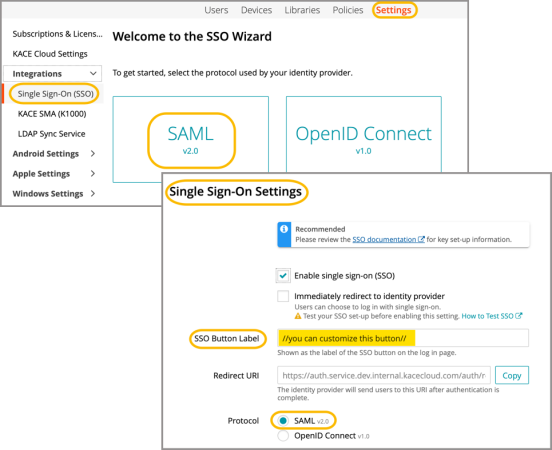
Learn more about SAML-based SSO using Okta.
Usability Enhancements
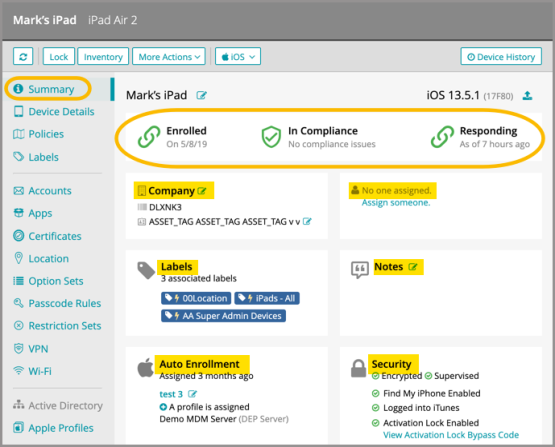
New Devices Summary Tab
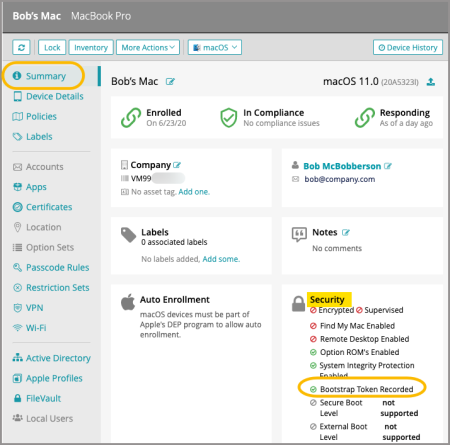
The new Summary tab is a one-stop overview of the key functional details on single or multiple devices. Functions include: Enrollment and compliance status, company details, user details, label association, notes, auto-enrollment status, and key security details.
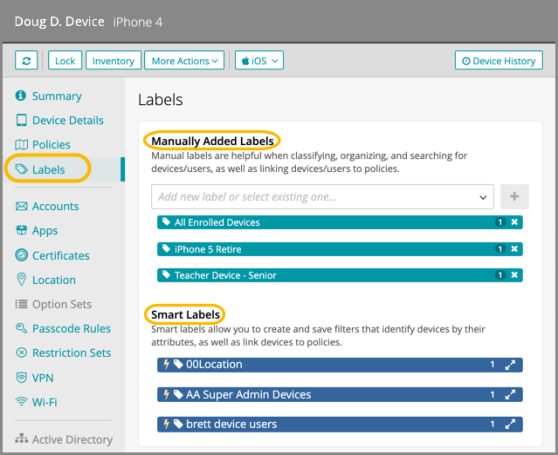
Redesigned Labels tab
Our existing labels tab in the devices workflow has been redesigned with a simplified, scannable layout that brings more information up front.
Functionality
Schedule OS Update
The schedule OS Update function lets an admin select and schedule the OS update version for single or multiple devices. Starting with macOS 11.0, admins will also be able to push OS updates to manually enrolled macOS devices in addition to DEP enrolled devices.
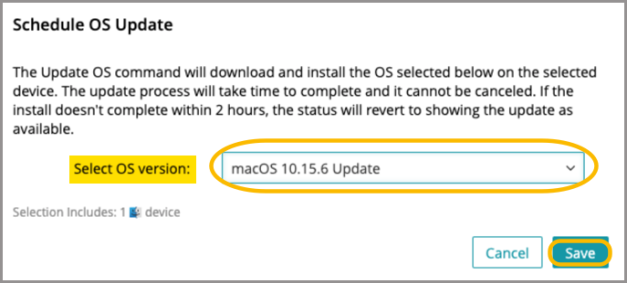
Learn more about device functionality.
Bootstrap Tokens for Manually Enrolled Devices
When a manually enrolled macOS (10.16, 11.0) or iOS device is upgraded, it will now store a bootstrap token in KACE Cloud MDM. This will enable users to use their Active Directory credentials to log in to a FileVault-encrypted device.
New Restriction Settings
iOS 14.0+ Devices - Admins can now choose whether or not to allow App Clips on devices.
macOS 11.0 Devices - macOS 11.0 devices now have access to the 'Automatically advance Setup Assistant screens' option that was previously only available for tvOS.
DEP Profiles - Admins now have the ability to enable/disable specific skip screens for end users during the DEP enrollment process.
Certificates
Certificates used for identity and encryption that are in the PKCS12 format—files with .pfx or .p12 extensions, can now be uploaded and deployed directly to devices or as associated with certain VPN or Exchange Account configurations.
Resolved Issues
Bug fixes are included in the resolved issues list for two release periods and are then retired.
| Issue | Description | Status |
| ESMCL - 4271 Android Wi-Fi autojoin not working on Android 9+. | Fixed in agent. Android Wi-Fi auto-join now working on Android 9+. |
FIXED |
| ESMCL - 4251 Cannot select 'Skip iMessage and FaceTime' in DEP Profile screen. | Can accurately select 'Skip iMessage and FaceTime' checkbox. | FIXED |
| ESMCL - 4236 Installing app directly on device from Playstore installs every app in the library. | Now installs only the apps selected on the PlayStore import screen. |
FIXED |
| ESMCL- 4171Outlook recently removed published app configuration, but setting the configuration continues to work. | Microsoft has fixed this on their end. |
FIXED |
| ESMCL- 4041 Incorrect device history when installing apps across different operating systems | When device history shows an "installing application" record for the app, no additional history is included. | FIXED |
| ESMCL- 4031 App list when importing to device does not show app configs | The list of apps available for adding includes one item for every App + App Config combination. |
FIXED |
| ESMCL- 3852 Clearing search filter on users page does not update results | The user list updates to show all users and not just the ones that match the search. | FIXED |
| ESMCL- 3507 Device History does not show the installation of Android Options | Device History screen shows the installation of the android options configuration |
FIXED |
Known Issues
Additional Resources
Getting Started with KACE Cloud MDM
© 2020 Quest Software Inc.
ALL RIGHTS RESERVED.
This guide contains proprietary information protected by copyright. The software described in this guide is furnished under a software license or nondisclosure agreement. This software may be used or copied only in accordance with the terms of the applicable agreement. No part of this guide may be reproduced or transmitted in any form or by any means, electronic or mechanical, including photocopying and recording for any purpose other than the purchaser’s personal use without the written permission of Quest Software Inc.
The information in this document is provided in connection with Quest Software products. No license, express or implied, by estoppel or otherwise, to any intellectual property right is granted by this document or in connection with the sale of Quest Software products. EXCEPT AS SET FORTH IN THE TERMS AND CONDITIONS AS SPECIFIED IN THE LICENSE AGREEMENT FOR THIS PRODUCT, QUEST SOFTWARE ASSUMES NO LIABILITY WHATSOEVER AND DISCLAIMS ANY EXPRESS, IMPLIED OR STATUTORY WARRANTY RELATING TO ITS PRODUCTS INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTY OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE, OR NON-INFRINGEMENT. IN NO EVENT SHALL QUEST SOFTWARE BE LIABLE FOR ANY DIRECT, INDIRECT, CONSEQUENTIAL, PUNITIVE, SPECIAL OR INCIDENTAL DAMAGES (INCLUDING, WITHOUT LIMITATION, DAMAGES FOR LOSS OF PROFITS, BUSINESS INTERRUPTION OR LOSS OF INFORMATION) ARISING OUT OF THE USE OR INABILITY TO USE THIS DOCUMENT, EVEN IF QUEST SOFTWARE HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. Quest Software makes no representations or warranties with respect to the accuracy or completeness of the contents of this document and reserves the right to make changes to specifications and product descriptions at any time without notice. Quest Software does not make any commitment to update the information contained in this document.
If you have any questions regarding your potential use of this material, contact:
Quest Software Inc.
Attn: LEGAL Dept.
4 Polaris Way
Aliso Viejo, CA 92656
Refer to our website (www.quest.com) for regional and international office information.
Patents
Quest Software is proud of our advanced technology. Patents and pending patents may apply to this product. For the most current information about applicable patents for this product, please visit our website at www.quest.com/legal.
Trademarks
Quest and the Quest logo are trademarks and registered trademarks of Quest Software Inc. in the U.S.A. and other countries. For a complete list of Quest Software trademarks, please visit our website at www.quest.com/legal. All other trademarks, servicemarks, registered trademarks, and registered servicemarks are the property of their respective owners.